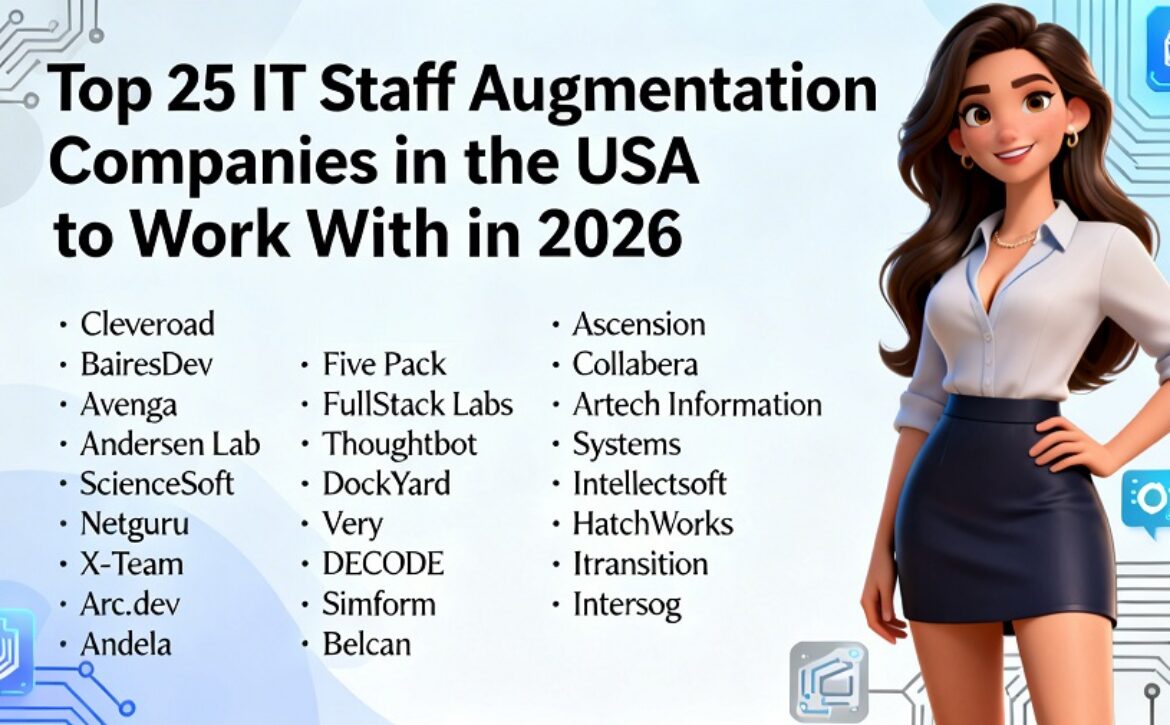
Top 25 IT Staff Augmentation Companies in the USA to Work With in 2026
Finding skilled software developers to fill these roles has become one of the biggest challenges faced by technology-based businesses. As organizations of all sizes across all sectors build new digital products, modernize current legacy systems and implement cloud-based technologies, there is increasing need for highly skilled, experienced engineers.
With traditional hiring methods, it can take employers several months to identify and onboard qualified developers. In many competitive markets, it is difficult to find qualified candidates who are available for immediate hire. For organizations that need to move quickly, this creates a significant bottleneck in product development.
IT staff augmentation has become a viable alternative to traditional hiring practices. Rather than spending several months interviewing job candidates and searching for permanent employees, employers can augment their current team with skilled developers who have experience with the specific type of work being performed on that project, allowing for immediate contributions to the team.
This type of approach provides organizations with the ability to scale up their engineering workforce when needed, access specialized technical skills, and provide their developers with flexibility to adapt to changing project scope.
Many companies have implemented IT staff augmentation models to reduce development timelines while still maintaining quality engineering standards and processes.
There are many companies in the U.S. that provide IT staff augmentation and dedicated development teams. Some focus on enterprise software and digital transformation initiatives; some target startups, SaaS and emerging technology markets (i.e., artificial intelligence and cloud computing).
The below information includes a few of the top-rated IT Staffing augmentation firms that provide IT Staff augmentation solutions and solutions to U.S.-based business partners to assist them with developing a greater engineering resource capacity, delivering combined digital products that are complex successfully.
1. Cleveroad
Established: 2011
Based in: New York, USA
Pricing range: $25–$49 per hour
Domain expertise: Web development, mobile applications, AI solutions, cloud platforms, enterprise software
Reviews: 70+ reviews on Clutch, average rating 4.9/5
Cleveroad is a software development company that helps startups and enterprises expand their engineering teams with experienced developers, QA engineers, and DevOps specialists. Founded in 2011, the company works with organizations across industries such as healthcare, fintech, logistics, retail, and media.
Businesses often collaborate with Cleveroad to scale development teams quickly while maintaining full control over product strategy and project management. Companies looking to expand their internal teams frequently rely on it staff augmentation services to access skilled engineers and accelerate software development without long recruitment cycles.
Their engineers specialize in building scalable digital products, cloud-based platforms, and modern web and mobile applications.
2. BairesDev
Established: 2009
Based in: San Francisco, USA
Pricing range: $50–$100 per hour
Domain expertise: Software development, AI, cloud platforms, mobile applications, data engineering
Reviews: 500+ reviews on Clutch, average rating 4.9/5
BairesDev is a nearshore software development company that provides services to companies in the United States and connects them with skilled professionals in Latin America. BairesDev also provides businesses with software teams that are located throughout Latin America, allowing them to easily build distributed software teams.
BairesDev’s staff augmentation services enable companies to grow their engineering capabilities quickly while providing ongoing support for both high-quality software development standards and excellent communications between all parts of the project team regardless of location.
3. Avenga
Established: 2019
Based in: New York, USA
Pricing range: $60–$120 per hour
Domain expertise: Digital engineering, cloud development, enterprise software, AI platforms
Reviews: 10+ reviews on Clutch, average rating 4.8/5
A Global Technological Partner such as Avenga helps businesses to develop current digital platforms as well as enterprise software solutions. Avenga provides staff augmentation teams to work closely with internal engineering groups.
Developers who work for Avenga have expertise in cloud infrastructures, data platforms, and scalable enterprise applications.
4. Andersen Lab
Established: 2007
Based in: Warsaw, Poland
Pricing range: $50–$99 per hour
Domain expertise: Web development, mobile development, QA, enterprise platforms
Reviews: 80+ reviews on Clutch, average rating 4.9/5
Andersen Laboratory offers a complete range of software development and dedicated engineering services to companies that create complicated digital systems. They provide assistance to organizations that need to increase their engineering staff by supplying them with highly capable engineers through their staff augmentation services.
Andersen has developed a reputation for providing excellent software development methodologies and developing long-term relationships with large corporations.
5. ScienceSoft
Established: 1989
Based in: Texas, USA
Pricing range: $50–$99 per hour
Domain expertise: Enterprise software, cybersecurity, data analytics, healthcare IT
Reviews: 30+ reviews on Clutch, average rating 4.8/5
With multiple decades of experience, ScienceSoft is one of the most established IT consulting and software development companies. They have a proven ability to deliver enterprise solutions through their development teams and technical skillset for organisations that create major software platforms.
Engineering at ScienceSoft typically includes enterprise systems, cybersecurity solutions, advanced data analytics platforms and other related fields.
6. Netguru
Established: 2008
Based in: Poznan, Poland
Pricing range: $50–$99 per hour
Domain expertise: Web development, fintech platforms, mobile applications, product design
Reviews: 60+ reviews on Clutch, average rating 4.8/5
Well-known within the software development industry, Netguru provides services to startups, scale-ups & global corporations. They create dedicated development teams to support product design and development, engineering, and develop responsive digital product strategies.
With their staff augmentation model, organizations can seamlessly add new experienced developers to their internal teams.
7. X-Team
Established: 2004
Based in: Melbourne, Australia
Pricing range: $50–$99 per hour
Domain expertise: Remote engineering teams, frontend frameworks, backend systems
Reviews: 20+ reviews on Clutch
X-Team is dedicated to establishing top quality remote engineering teams for tech companies. Through its network, they provide businesses with developer resources that possess both modern technology experience as well as expertise in scalable application architecture.
X-Tech has earned the trust of a multitude of large global technology firms to help them expand their teams of engineers while still employing a distributed development model.
8. Arc.dev
Established: 2019
Based in: San Francisco, USA
Pricing range: $60–$120 per hour
Domain expertise: Remote developer hiring, software engineering, frontend and backend development
Reviews: Platform-based reviews from hiring clients
Companies can find pre-vetted remote engineers through Arc.dev, which is an online developer recruitment site. Businesses use Arc to source qualified developers for either short project assignments or long-term engineering positions. The focus of Arc’s business model is to allow companies to rapidly grow their engineering teams without having a complicated hiring experience.
9. Andela
Established: 2014
Based in: New York, USA
Pricing range: $50–$100 per hour
Domain expertise: Distributed engineering teams, cloud software, full-stack development
Reviews: 70+ reviews across industry platforms
Andela is an international technology talent marketplace that helps match businesses with skilled engineers from throughout the globe. Andela’s platform allows companies to form global distributed teams that have experienced engineers with specific types of technical skills.
Numerous start-ups and established businesses have relied on Andela to find the best global engineering talent and expedite their software development process.
10. Adeva
Established: 2015
Based in: San Francisco, USA
Pricing range: $50–$100 per hour
Domain expertise: Remote development teams, SaaS platforms, web applications
Reviews: 20+ reviews on Clutch
Through Adeva’s services, businesses can find remote developers for their staff and also build distributed engineering teams. The company has put an emphasis on connecting businesses to software engineers that have relevant experience and skill sets and can work seamlessly as part of their product teams.
The software developers that Adeva connects businesses with support projects in the area of Software as a Service (SaaS) platforms, web applications, and cloud infrastructure solutions.
11. Five Pack
Established: 2008
Based in: Texas, USA
Pricing range: $100–$149 per hour
Domain expertise: Mobile app development, SaaS products, web platforms, digital product engineering
Reviews: 30+ reviews on Clutch
The basis of Five Pack is the United States and are a developer of software to facilitate an organisation’s ability to create and develop cutting-edge digital products. Five Pack’s engineers support every type of project, from mobile application creation to the development of complex Software As A Service (SaaS) Platforms.
When organisations want to partner with Five Pack, they do so because they have experience with both product strategy and the technical implementation of a product.
12. FullStack Labs
Established: 2013
Based in: California, USA
Pricing range: $50–$99 per hour
Domain expertise: Web development, React applications, Node.js platforms, cloud infrastructure
Reviews: 80+ reviews on Clutch
FullStack Labs develops teams of developers proficient in contemporary web/mobile technologies. Their mission is to assist companies in developing scalable digital products by supplementing their engineering staff with expert developers.
Many of the projects they’re engaged with consist primarily of SaaS (Software as a Service), enterprise and cloud-based applications.
13. Thoughtbot
Established: 2003
Based in: Boston, USA
Pricing range: $150–$199 per hour
Domain expertise: Product design, web development, digital product strategy
Reviews: 30+ reviews on Clutch
Thoughtbot provides professional product development consulting services to both startups and established businesses. Each of their project teams delivers a combination of product strategy, user experience design and engineering expertise to assist their clients in delivering premium-quality digital products.
A variety of organizations use Thoughtbot as a partner to enhance their early-stage product development or to launch new digital platforms.
14. DockYard
Established: 2010
Based in: Massachusetts, USA
Pricing range: $150–$199 per hour
Domain expertise: Web applications, frontend development, product design, scalable platforms
Reviews: 20+ reviews on Clutch
DockYard develops web apps and large-scale software platforms. Their clients rely on them for engineering and product development to help accomplish their goals. Their teams frequently assist in projects that are complex and in need of frontend frameworks or enterprise-level systems.
15. Very
Established: 2011
Based in: Tennessee, USA
Pricing range: $150–$199 per hour
Domain expertise: IoT development, cloud infrastructure, data platforms, enterprise software
Reviews: 15+ reviews on Clutch
Very provides consulting services to organizations developing connected products and utilizing data to make data-driven decisions as part of their technology. Very’s engineers have experience working with IoT ecosystems, creating cloud architectures, and developing very complex distributed systems in many different types of projects.
When businesses develop advanced technological solutions that require significant engineering expertise, they often collaborate with Very.
16. DECODE
Established: 2016
Based in: Zagreb, Croatia
Pricing range: $50–$99 per hour
Domain expertise: Mobile applications, web platforms, digital product development
Reviews: 20+ reviews on Clutch
DECODE is a digital product company dedicated to developing mobile apps and web-based software for startups and established businesses. The staff at DECODE include experienced software engineers with backgrounds in developing mobile applications and creating large-scale web applications for organizations. In addition to providing technical services, DECODE also supports companies by helping them improve their internal processes and speed up the time-to-market of their products.
17. Simform
Established: 2010
Based in: Florida, USA
Pricing range: $25–$49 per hour
Domain expertise: Cloud-native applications, microservices architecture, DevOps, enterprise platforms
Reviews: 70+ reviews on Clutch
Simform helps companies speed up software development and modernize their digital infrastructure through the use of its engineering teams. They provide developers who are skilled in cloud platforms, building microservices-based applications, and developing scalable applications.
Their clientele includes both start-ups and corporations looking for additional flexible engineering bandwidth.
18. Belcan
Established: 1958
Based in: Ohio, USA
Pricing range: Enterprise consulting rates
Domain expertise: Engineering consulting, aerospace systems, software engineering
Reviews: Enterprise clients across multiple industries
The company’s primary markets include Aerospace, Automotive, and Manufacturing. Belcan’s engineering teams have supported clients developing advanced technical systems and large-scale systems and projects.
19. Ascension
Established: 2002
Based in: Texas, USA
Pricing range: Varies by project
Domain expertise: IT staffing, technology consulting, workforce management
Reviews: Enterprise client partnerships
Ascension is a provider of IT staffing and consulting solutions for companies looking for experienced technology professionals. Ascension helps companies to develop development teams and manage workforce resources for large technical projects. Their services are frequently used by companies undergoing digital modernization initiatives.
20. Collabera
Established: 1991
Based in: New Jersey, USA
Pricing range: Enterprise pricing models
Domain expertise: Cloud computing, enterprise software, data engineering, IT consulting
Reviews: 50+ reviews across industry platforms
Collabera is a global technology consulting and staffing company that provides technical professionals for enterprise digital initiatives. The company supports projects involving cloud infrastructure, data platforms, and enterprise software development.
Large organizations often rely on Collabera to scale technology teams and deliver complex digital transformation programs.
21. Artech Information Systems
Established: 1992
Based in: New Jersey, USA
Pricing range: Enterprise staffing rates
Domain expertise: IT staffing, digital engineering, consulting services, enterprise workforce solutions
Reviews: 20+ reviews across industry platforms
Artech Information Systems has a worldwide focus on IT hiring and consulting. They work with all types of companies, (e.g., healthcare, finance, telecommunications), to find experienced technology workers to help with complex digital solutions. Most companies call on Artech when trying to expand their engineering team, when they need support for large information technology projects, or if they need to find workers with specialty technical skills when there aren’t enough personnel available internally.
22. Intellectsoft
Established: 2007
Based in: New York, USA
Pricing range: $50–$99 per hour
Domain expertise: Enterprise platforms, blockchain development, cloud software, digital transformation
Reviews: 40+ reviews on Clutch, average rating around 4.8/5
Intellectsoft is a software development and consulting firm that provides technology consulting services to organizations looking to modernize their digital infrastructure and develop enterprise-grade applications. The organization has specialists in engineering that focus on the development of enterprise mobility solutions, cloud computing, and blockchain technology.
Intellectsoft is commonly chosen by businesses as a partner to help develop teams with extensive experience in the development of large-scale enterprise software solutions.
23. HatchWorks
Established: 2016
Based in: Georgia, USA
Pricing range: $50–$99 per hour
Domain expertise: Cloud development, AI platforms, product engineering, digital transformation
Reviews: 20+ reviews on Clutch
HatchWorks is a tech consulting firm that develops modern digital platforms & dev teams for businesses. That means the company is all about providing the software solutions through the use of cloud infrastructure and data technologies.
Collaboration with HatchWorks can help organizations through product development at a rapid pace through the implementation of modern engineering practices.
24. Itransition
Established: 1998
Based in: Denver, USA
Pricing range: $50–$99 per hour
Domain expertise: Enterprise software development, data analytics, cloud platforms, IT consulting
Reviews: 40+ reviews on Clutch, average rating around 4.9/5
Itransition is an international provider of developing and consulting services in software engineering for enterprise organisations. Itransition mainly partners with those organisations who need scalable digital systems and sophisticated data solutions.
Itransition engineers guarantee excellent support for all projects concerned with enterprise platforms, cloud-based application solutions, as well as the development of complex digital ecosystems.
25. Intersog
Established: 2005
Based in: Chicago, USA
Pricing range: $50–$99 per hour
Domain expertise: Web development, mobile applications, AI solutions, product engineering
Reviews: 20+ reviews on Clutch
Intersog offers development teams and augmented staff to help firms create digital products. We aid businesses in growing their engineering capabilities through having seasoned developers added to internal engineering functions.
The developers working for Intersog work on software projects that include webpages, mobile apps, and some newer tech (AI).
Conclusion
Across all industries, many businesses continue experiencing difficulty finding skilled software engineers. As technology continues to evolve and products become more complex, businesses are needing new and flexible ways to expand their engineering capacity due to the shortened timelines required for developing new products.
Utilizing IT staff augmentation (outsourcing software development) is one of the best solutions to provide options to solve your problem of never having enough engineers to complete your projects. Partnering with an external firm that provides software developers means that companies can quickly find the right people with the proper skill set to build out their teams based on current project needs and how quickly those projects need to be done.
The companies below are considered some of the top options for companies looking to augment their staff through IT staff augmentation services in the United States. Each of these companies has specific areas that they excel in, such as enterprise-level software development or working with small start-up companies on developing new products using emerging technologies.
The company you choose to partner with to augment your staff will depend on your organization’s project goals, project requirements, and technology stack, as well as your company’s long-term product goals. By having a solid staff augmentation strategy implemented, many organizations can speed up product development timelines, increase the quality of their products, and provide the necessary flexibility to compete in the rapidly changing digital marketplace.